Vulnerability Lifecycle
Understanding software vulnerabilities is a key aspect of cyber security
14 papers and 8 talks
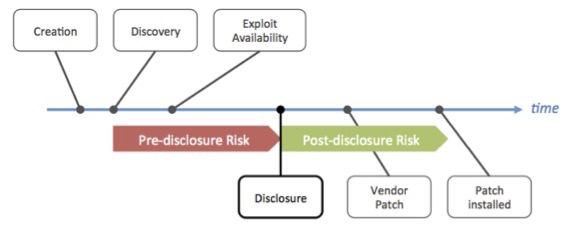
Technical advancements within software design and development have not prevented the release of insecure software and consequently the appearance of vulnerabilities. Economic and other non-technical incentives increasingly are perceived as the primary reasons for today’s heightened risk exposure. The life cycle of a vulnerability can be divided into phases between distinct events such as “discovery”, “disclosure”, etc. Each phase reflects a specific state of the vulnerability and the associated risk exposure for the users of the affected software. I analyzed the evolution of the vulnerability lifecycle of thousands of vulnerabilities over the past decades.
Papers
-
Paper - Bug Bounty Program of Last Resort »»
This paper makes the case for a centralized Bug Bounty Program of Last Resort to cover critical open-source projects and smaller vendors, who cannot fund them.
| Published: Feb 2021 | Available: Paper (en) » -
Paper - International Vulnerability Purchase Program (IVPP) »»
Cyber security depends largely on reporting vulnerabilities under the practices of coordinated disclosure. Meanwhile, the black market is expanding rapidly and offering large rewards for the same information. We examine the economics of depriving cyber criminals’ access to new vulnerabilities.
| Published: Dec 2013 | Available: Paper (en) » -
Paper - The Known Unknowns in Cyber Security »»
Vulnerabilities that are known only to privileged closed groups, such as cyber criminals, brokers, and governments, pose a real and present risk to all who use the affected software.
| Published: Dec 2013 | Available: Paper (en) » -
Paper - Vulnerability Threat Trends 2012 »»
Despite massive security investments of the software industry, vulnerability disclosures have risen considerably in 2012.
| Published: Feb 2013 | Available: Paper (en) » -
Paper - Secunia Yearly Report 2011 »»
The Secunia Yearly Report 2011 focuses on the evolution and threats of software vulnerabilities, software vulnerability exploits, and the challenges involved in protecting private users and corporate infrastructures reliant on information technology.
| Published: Feb 2012 | Available: Paper (en) » -
Paper - Familiarity Breeds Contempt »»
Our analysis of a decade of software vulnerability (both open and closed source), shows that properties extrinsic to the software play a much greater role in the rate of vulnerability discovery than do intrinsic properties such as software quality.
| Published: Dec 2010 | Available: Paper (en) » -
Paper - The Security Exposure Of Software Portfolios »»
We examine the software portfolio of the average user based on empirical data from over two million users frequently scanning their systems with Secunias Personal Software Inspector (PSI).
| Published: Mar 2010 | Available: Paper (en) » -
Paper - Why Silent Updates Boost Security »»
Security updates don’t benefit the end user of software if the update mechanism and strategy is not effective. In this paper we analyze the effectiveness of different Web browsers update mechanisms based on massivle Google web log data.
| Published: May 2009 | Available: Paper (en) » -
Paper - Firefox (In)Security Update Dynamics Exposed »»
How (in)secure is your Internet browser? You never know. One way to know more is to look at how frequently it gets updated. With data from Google’s search logs we analyze the time series of update installs to compare the security of browsers.
| Published: Jan 2009 | Available: Paper (en) » -
Dissertation - Security Econometrics - The Dynamics of (In)Security »»
In this dissertation we claim that knowledge of the vulnerability lifecycle (the vulnerability discovery-, exploit-, disclosure-, and patch-time) allows us to distinguish major processes in the security environment and to quantify the risk exposure and evolution thereof at macroscopic level.
| Published: Jan 2009 | Available: Dissertation (en) » -
Paper - Understanding The Web Browser Threat »»
Access to Google’s global Web server logs enabled us to provide the first in-depth global perspective on the state of insecurity for Web browser technologies. Understanding the nature of the threats against Web browser and their plug-in technologies is important for continued Internet usage.
| Published: Aug 2008 | Available: Paper (en) » -
Paper - Putting Private And Government CERT’s To The Test »»
By monitoring relevant security sites on 30-minute intervals for more than 18 months, we collected a unique dataset to compare CERT’s and private offerings.
| Published: Jul 2008 | Available: Paper (en) » -
Paper - Exposing Vendors (In)security Performance (0-Day Patch) »»
We evaluated the patch development process of Microsoft and Apple using publicly available vulnerability data from 2002 to 2007. By correlating information from multiple sources, we analyzed possible bias in vendor information.
| Published: Mar 2008 | Available: Paper (en) » -
Paper - Large-Scale Vulnerability Analysis »»
Analyzing over 80,000 security advisories, we determined the discovery-, disclosure-, exploit-, and patch-date of the vulnerabilities. We quantify the trend towards zero-day exploits and measure the gap between exploit- and patch-availability.
| Published: Sep 2006 | Available: Paper (en) »
Talks
-
Keynote - BSides HH - Hamburg 2014
The Known Unknowns & Outbidding Cyber Criminals
Hamburg, Dec 2014
| Event: www.securitybsides.com ..
| Slides: bsides_known_unknows_outbidding_criminals_2014.pdf -
Talk - ISSS Security Lunch
The Known Unknowns & Outbidding Cyber Criminals
Zurich, Sep 2014
| Event: isss.ch .. -
Talk - ISD Internet Security Days 2014
The Known Unknowns & Outbidding Cyber Criminals
Brühl - Köln, Sep 2014
| Event: www.eco.de .. -
Talk - Area 41 Security Conference
International Vulnerability Purchase Program
Zurich, May 2014
| Event: area41.io ..
| Slides: area41_known_unknows_outbidding_criminals_2014.pdf -
Talk - RSA Conference Vendor Briefings
Cybercrime Kill Chain & Vulnerability Threat Trends
San Francisco, Mar 2013
| Event: www.rsaconference.com .. -
Talk - SwissSign-Event «Sicherheit in der digitalen Welt»
Trickbetrüger im Internet - von Phishing, Spam und organisiertem Verbrechen
Zurich, Sep 2008
| Event: www.swisssign.com .. -
Talk - BlackHat Europe Briefings
0-Day-Patch Exposure - Exposing vendors patch performance
Amsterdam, Mar 2008
| Event: www.blackhat.com ..
| Slides: blackhat_0day_patch_dynamics_2008.pdf -
Talk - BlackHat USA Briefings
The speed of (in)security
Las Vegas, Aug 2006
| Event: www.blackhat.com ..
| Slides: blackhat_speed_of_insecurity_2006.pdf